Originally posted to LinkedIn on May 15, 2017
In late April 2017, a hacker calling himself “The Dark Overlord” claimed to have released the first 10 episodes of the new season of “Orange is the New Black” after Netflix failed to meet his ransom demands.
This is just one of the latest and most high profile instances of a ransomware attack. 2016 was a banner year for this fast-growing form of malware. According to IT security consultant SonicWall, the number of ransomware attacks during the year was 167 times the number of attacks in 2015.
And, ransomware attacks can be extremely costly. Last year. an IBM survey found that 46% of surveyed executives had encountered ransomware in the workplace, and that 70% of that group had paid to get data back. For nearly 50% of the executives that paid, the ransom was $20,000 or more. In one of the most notable 2016 attacks, a California hospital had its internal computer system shut down by hackers who demanded $3.7 million in ransom.
How do you combat ransomware? Let’s start with defining the challenge.
What is ransomware?
Ransomware has been around since the 1990s. But, its growth has exploded in recent years. In a typical attack by the most common type of ransomware, called a Trojan, victims receive an e-mail with an attachment or URL that appears legitimate. But, the attachment actually contains the ransomware software; or the URL, when clicked upon, directs the victim to a website that infects their computer with the malicious software.
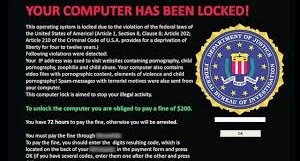
The ransomware then begins encrypting files on local drives, backup drives – even other computers on the same network that the victim’s computer is attached to. The victim will no longer have access to their data and will soon see messages on their computer demanding a ransom payment – usually with bitcoins – in exchange for a decryption key that will enable them to retrieve their “hostaged” files.
In a Trojan ransomware attack, there’s almost nothing that can be done to get rid of the malicious software, which is why you read so many news accounts about companies paying tens of thousands of dollars to retrieve their files or data.
Other types of ransomware
Scareware is a bit of a “paper tiger.” It is a form of malware that tricks a user into downloading what appears to be a legitimate antivirus application. Using Windows-style popups, the software tells victims that their PC has been infected with a virus that doesn’t actually exist, scaring the victim into paying to solve the imaginary threat.
If scareware appears when you’re browsing a website, it most likely means that the website has been compromised. Close your browser immediately and run a full anti-virus scan – and don’t revisit that website.
Another type of ransomware is leakware, also known as doxware. Leakware employs a blackmailing attack that threatens to publish victims’ stolen information rather than deny them access to the compromised computer. In a leakware attack, malware extracts and sends sensitive information back to the attacker, who threatens to make the information public unless the victim pays the ransom.
What kinds of companies are at greatest risk of a ransomware attack?
Companies, both large and small, can be the targets of ransomware attacks. Healthcare organizations are at particular risk because of the personal health and financial information in their digital health records. In addition, these organizations, generally, are not as rigorous in their security efforts as financial services firms – a field that would seem ripe for hacking. But, because financial services firms are tightly regulated and are logical targets for hacking, the industry as a whole has one of the strongest records when it comes to IT security. The same cannot be said for other sectors that frequently struggle with internal budget issues such as education and state and local governments.
Manufacturers are an increasing target of corporate espionage – efforts to steal intellectual property such as trade secrets, manufacturing process data or operational reports. Many of these attacks come from countries such as China and those in Eastern Europe.
What can organizations do to defend themselves?
Organizations should take a two-pronged approach to defending themselves from ransomware: education/prevention and security backup.
- Education and prevention: Implement awareness training for employees and robust technical prevention controls. Educate employees about not clicking on attachments and URLs with which they are unfamiliar. Once a ransomware attack has occurred, there’s little that can be done – except to pay the ransom.
- Security backup: Create a solid business continuity plan in the event of a ransomware attack, including creating redundancy into a secure cloud or secure server. Make sure you have an incident response plan that outlines various hacking scenarios.
Lastly, NoMoreRansom.org is a website that provides additional helpful guidance on preventing ransomware attacks.
For most organizations, following these guidelines will significantly improve IT security – potentially saving tens to hundreds of thousands of dollars. Or, schedule a consultation with one of our experts today.




